When determining or reviewing a facility’s security policy and compliance, many industries find that mobile information devices are an increasingly relevant attack vector to plan for and mitigate. As consumer technology becomes more capable and covert, it is important to consider use cases in which detection of unauthorized mobile phones could be beneficial to your organization.
Call Center Security

Modern call centers can be busy places with many employees each working tens of accounts per day. To protect valuable customer data, many call centers do not allow employees to use personal devices while at work. Cell phone detection devices can be used to enforce this policy and prevent unauthorized use of mobile information devices in these facilities.
Risks that can be mitigated with cell phone detection include the capturing of computer screens via phone cameras, recording internal communications or conversations with customers, and the transmission of these files off-site. For prevention of these outcomes, it is essential for secure facilities such as call centers to ensure personal cell phones and other transmission devices are not used covertly.
Industrial Safety and Manufacturing
The unauthorized use of cell phones and other transmission devices in an industrial settings can have many repercussions. Firstly, there are issues of safety: distracted employees can create safety hazards for both themselves and fellow employees. Sensitive industrial and manufacturing equipment can be sensitive to RF transmissions and electro-magnetic radiation. Routine handling of personal devices can permit the spread of bacteria and viruses when dirty devices are used in a clean environment – especially where food is manufactured and prepared.
Implementing a cell phone detection system allows industrial settings to contain device usage to authorized devices, mitigating these potential safety and health hazards. If transmission activity is picked up, it can be used to create a profile of what times the phones were used, the vicinity of use, and types of signals – such as the frequency and signal strength. This can all be used to give actionable intelligence to security staff, who in turn can find the devices.
Compliance in Corporate Settings

No modern corporation wants to take risks with their data. Classified information can be protected through authorization and authentication procedures, but can be further physically protected through the detection of unrecognized cell phones and hidden RF transmission devices that might otherwise permit unauthorized access.
Today’s mobile devices are multi-tasking toolsets that can send text messages, take pictures, and record or transmit audio and video. Their sophisticated features and small size make them the perfect tool for industrial espionage, for which they can be used to record and steal valuable and sensitive information.
Protect and secure intellectual property (IP), techniques, and processes by implementing device policies backed by a robust cell phone detection system.
Prisons and Correctional Facilities
Contraband cell phone use has skyrocketed in recent years in prisons and correctional facilities. This can create a major safety and security problem for both staff and inmates. Criminal organizations may continue to operate illegal activity remotely from within the walls of these facilities.
In the United States, Congress has passed the Contraband Cell Phone Act, which prohibits the possession of cell phones in prisons by unauthorized persons, including inmates. However, this does not prevent the phones from being used, only allowing for stiff penalties if they are detected. Cell phone detection solutions can be used to monitor for use of these contraband phones.
SCIFs
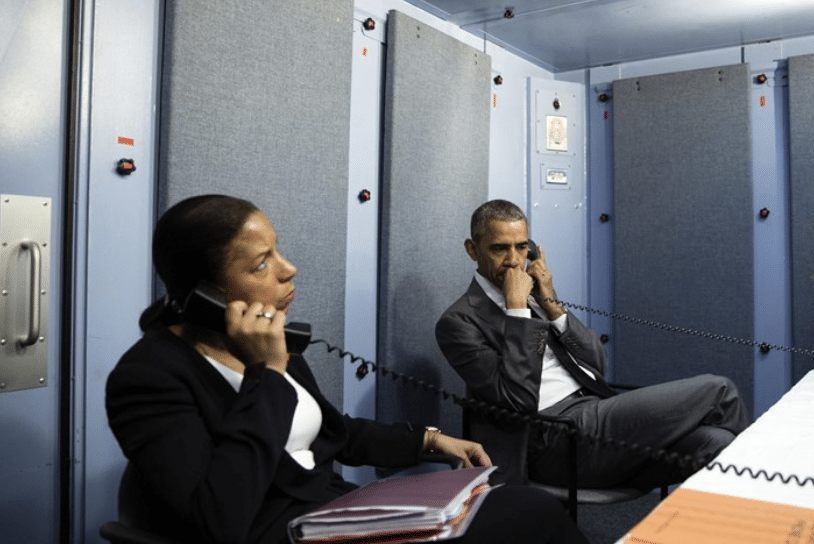
A sensitive compartmented information facility in U.S. military, national security/national defense and intelligence parlance, is an enclosed area within a building that is used to process sensitive compartmented information (SCI).
SCIFs can be either permanent or temporary and can be set up in official government buildings, in private residences of officials, or in hotel rooms and other places of necessity for officials when traveling or during emergency situations
Cell phones and other mobile devices need to be detected in case they are brought into a SCIF without authorization. This is to ensure the integrity of security and keep the sensitive information secure from being recorded or transmitted to outside the SCIF.
Education and Testing
Testing centers and education settings continue to have issues with improper use of cell phones. Phones can be used to cheat on exams – such as in motor vehicles departments, or large testing halls where professional exams are taking place. Some of these exams can cost hundreds of thousands of dollars to produce, and if compromised by cell phones can create huge losses as well as the integrity of the whole testing process.
Cell phone detection can prevent some of these issues by ensuring sure no devices are present to record test materials during exams.
Private Property Intrusion Detection
Give security a leg up by detecting the presence of an intruder’s cell phone on your premises via mobile device signals. Proactively detect potential intruders or stowaways by detecting their cell phone signal. Prevent after-hours theft or property damage.
With more than 9 out of 10 Americans owning a cell phone, the chances are good than any intruder will be carrying one. While they are highly convenient, their sophisticated features also make them a great spying tool that could be used to record and steal classified information.
Cellbusters’ Zone Protector is a powerful, easy-to-deploy, and cost-effective device that constantly scans for cell phone activity and can immediately alert security staff to the presence of an intruder. Zone Protector detection is not limited to line-of-sight or to the perimeter of premises, making it the ideal complement to infrared motion detectors and door and window sensors.






